Prologue: The Student Who Wasn’t There
The first clue wasn’t dramatic.
It didn’t arrive with sirens or subpoenas.
Machine Learning & Artificial Intelligence
00:00
00:00
01:31
It arrived as a complaint.
“Why am I waitlisted,” the email read, “for a class with 32 seats when only 18 students show up?”
Professor Daniel Reyes stared at the message on his screen. It was 8:12 a.m., and half the chairs in his Intro to Microeconomics class were empty. Not occasionally empty. Consistently empty.
Eighteen students attended regularly.
Thirty-two were enrolled.
Discover more
Educational Resources
Primary & Secondary Schooling (K-12)
Telescope
Fourteen names. No faces.
At first, he assumed laziness. Community college students often worked double shifts, raised families, survived chaos. Attendance fluctuated.
But this felt different.
Every missing student had something in common: perfect paperwork, instant enrollment, financial aid approved within 48 hours.
And none had ever stepped foot in his classroom.
Three weeks later, Daniel Reyes would sit across from two federal agents who would tell him that his simple attendance log had just cracked open one of the largest education fraud schemes in American history.
Primary & Secondary Schooling (K-12)
But on that quiet morning, he only knew one thing.
Something wasn’t right.

Chapter One: The Pattern
Daniel wasn’t an investigator. He was an economist. Patterns were his comfort zone.
So he did what economists do.
He made a spreadsheet.
He tracked login activity. Assignment submissions. IP timestamps from the school’s online portal.
Education
The missing students submitted work—always just enough to avoid being dropped. Quizzes completed at 3:07 a.m. Discussion posts written in flawless but strangely generic English.
When he ran their essays through plagiarism software, nothing triggered.
Too original.
Too polished.
Too identical in tone.
Then came the anomaly.
Five different “students” had logged into the portal from the exact same IP address—located not in California, not even in the United States—but bouncing through encrypted overseas servers.
Daniel reported it to the college’s IT department.
Two days later, the IT director called him.
“Delete your spreadsheet,” she said.
He laughed. “Excuse me?”
“Delete it. And stop digging.”
That was the moment he realized this wasn’t about attendance.
This was about money.
Chapter Two: The Aid Pipeline
Federal financial aid is tied directly to enrollment. Each registered student unlocks grants, loans, and state funding allocations.
The more students enrolled.
The more money flows in.
What Daniel didn’t know yet was that across California’s community college system, enrollment had mysteriously surged—despite declining graduation rates and shrinking in-person attendance.
On paper, it looked like growth.
In classrooms, it felt like absence.
When Daniel refused to drop the issue, the college quietly reassigned him from two online-heavy courses. No explanation.
That’s when he contacted a former student—now working in cybersecurity—named Aisha Rahman.
She agreed to look at the login metadata.
Three nights later, she called him.
Her voice wasn’t calm.
“Dan… this isn’t five fake students.”
He swallowed. “How many?”
“Try thousands.”
Chapter Three: The Ghost Network
Aisha’s analysis revealed something chilling.
Automated enrollment bots were flooding application systems during off-peak hours. They used synthetic identities—real Social Security numbers paired with fabricated names, or vice versa.
AI-generated transcripts.
AI-written placement essays.
AI-powered chat responses.
The system wasn’t being hacked.
It was being used exactly as designed.
And it approved them.
Each fake student triggered financial aid disbursements—sometimes $3,000. Sometimes $7,500. Multiply that by tens of thousands.
The money moved quickly through prepaid debit cards and layered shell accounts before vanishing into international crypto wallets.
But here’s the twist.
The bots weren’t crude.
They were adaptive.
When colleges changed verification protocols, the bots evolved within days.
“This isn’t some random scam ring,” Aisha said. “This is organized. Industrial.”
Daniel asked the obvious question.
“Why hasn’t anyone noticed?”
She hesitated.
“They have.”
Chapter Four: The Closed-Door Meeting
Within weeks, federal investigators from the Department of Education’s Office of Inspector General contacted Daniel.
Primary & Secondary Schooling (K-12)
He expected gratitude.
Instead, he found tension.
“We’re aware of irregularities,” one agent said carefully.
“Irregularities?” Daniel snapped. “There are entire classes full of people who don’t exist.”
The agents exchanged glances.
Then one leaned forward.
“You’re not looking at a college-level problem, Professor. You’re looking at a system-level vulnerability.”
Across California, over 100,000 enrollments showed statistical anomalies.
The estimated loss? Approaching $1 billion.
Daniel felt dizzy.
“That’s impossible.”
“No,” the agent replied. “It’s scalable.”
Chapter Five: The Inside Question
As investigators traced digital fingerprints, patterns emerged pointing to international networks operating out of Bangladesh, Pakistan, Nigeria, and Eastern Europe.
But something didn’t add up.
Certain verification overrides—manual approvals—required internal access.
Some accounts bypassed identity checks entirely.
Which meant one thing:
Someone inside the system was helping.
When this detail leaked internally, Daniel’s laptop was remotely wiped.
Aisha’s cybersecurity firm was hit with a denial-of-service attack.
And Daniel received a message from an anonymous email address.
Stop.
You are not prepared for what this touches.
He reported it.
The agent’s response was colder than expected.
“You should consider stepping back.”
Chapter Six: The Whistleblower
Three months into the investigation, a college financial aid officer named Marisol Vega requested a private meeting.
She looked exhausted.
“They told us to process everything,” she said. “Enrollment numbers meant funding. Funding meant survival.”
“Who told you?” Daniel asked.
She hesitated.
“Higher than campus level.”
She described quiet directives. Pressure to avoid excessive scrutiny. “We can’t afford to reject students,” administrators would say.
Because rejecting meant losing state allocations.
And declining enrollment meant political fallout.
The fraud rings didn’t break the system.
They exploited its desperation.
But before Marisol could formally testify, she resigned abruptly.
Two days later, she vanished from public records.
No forwarding address.
No LinkedIn.
Nothing.
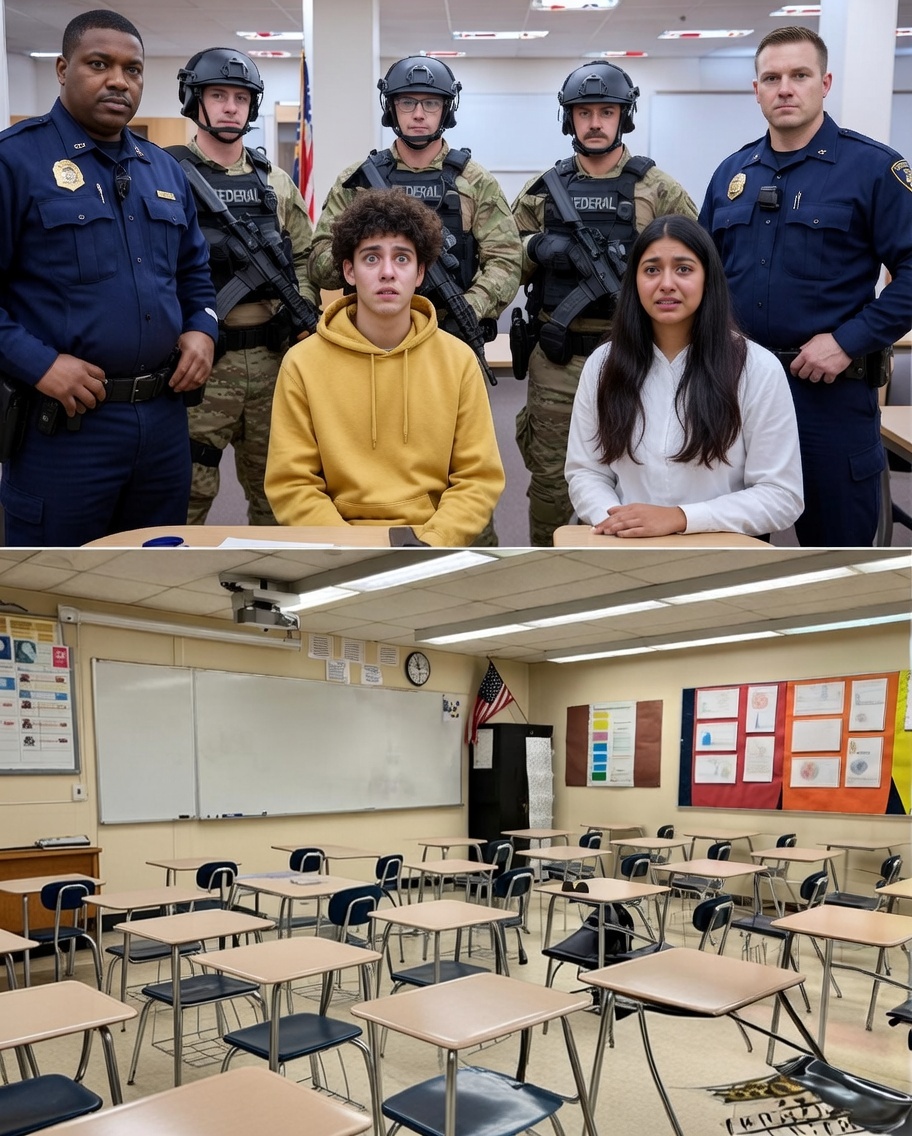
Chapter Seven: The Raid
At dawn, federal agents executed coordinated raids across multiple campuses and private residences tied to shell corporations handling aid disbursements.
Servers were seized.
Arrests made.
Headlines exploded:
$1 BILLION FRAUD EXPOSED
100,000 FAKE STUDENTS IDENTIFIED
The public saw victory.
Daniel saw fragments.
Because buried within the seized data was something unexpected.
A subfolder labeled:
Phase Two — Expansion
Chapter Eight: The Deeper Layer
Aisha decrypted portions of the recovered files.
The ghost enrollment protocol wasn’t limited to California.
It was being tested in other states. Adapted for unemployment benefits. Healthcare exchanges.
The architecture was modular.
Plug-and-play fraud.
And then they found the most disturbing line of code:
A machine learning feedback loop trained on institutional response times.
The system wasn’t just exploiting bureaucracy.
It was studying it.
Improving itself.
Daniel realized with a cold clarity that this wasn’t the end of something.
It was the prototype.
Chapter Nine: The Twist
One evening, Agent Holloway—the federal lead—met Daniel privately.
Off the record.
“What I’m about to tell you doesn’t leave this room,” Holloway said.
Daniel nodded.
“We traced initial vulnerabilities back five years. A pilot digital enrollment modernization grant.”
“Meaning?”
“Meaning parts of this infrastructure were built with federal innovation funding.”
Daniel stared at him.
“You’re saying the system that enabled the fraud… was funded to improve efficiency?”
Holloway didn’t answer directly.
But he didn’t deny it either.
Chapter Ten: The Vanishing Evidence
As prosecutions began, something strange happened.
Key evidence was sealed under national cybersecurity provisions.
Certain defendants disappeared from public dockets.
And references to international coordination quietly softened in official statements.
Daniel’s requests for transparency were denied.
His access to investigative updates revoked.
Then came the final blow.
An audit concluded that while “fraudulent activity occurred,” systemic institutional negligence was “unsubstantiated.”
Unsubstantiated.
A billion dollars gone.
Unsubstantiated.
Epilogue: The Empty Seat
Six months later, Daniel returned to teaching.
Primary & Secondary Schooling (K-12)
Enrollment numbers had stabilized.
Verification protocols strengthened.
But in his advanced economics class, one name caught his attention.
Registered.
Aid approved.
No attendance.
He checked the login timestamp.
3:07 a.m.
He ran the IP trace.
It bounced once. Twice.
Then stopped.
Location: Sacramento.
Not overseas.
Not foreign.
Domestic.
He felt the blood drain from his face.
Because this time—
The login credentials belonged to someone inside the Department of Education.
Daniel closed his laptop slowly.
Across the screen, a notification appeared.
Phase Two Initiated.
He wasn’t investigating a crime ring anymore.
He was staring at a system that had learned to protect itself.
And somewhere inside that system—
The ghosts were still enrolling.